Cybersecurity
8 posts in this category.
How to Recognize Phishing Emails
Phishing attacks steal millions of credentials a year by impersonating banks, vendors, and colleagues. Learn the seven warning signs that reveal a phishing email at a glance.
May 22, 2025 · Dejan Murko

Types of Malware Explained: What You Need to Know
Malware is software built to harm, exploit, or control devices and networks. Learn the major types — viruses, worms, ransomware, spyware, trojans, and rootkits — and how to defend.
Apr 17, 2025 · Dejan Murko
Cybersecurity Compliance Regulations
Cybersecurity compliance frameworks are designed for enterprises, but most controls scale down to SMBs. Here is how to map ISO, NIST, and CIS to a small-business reality.
Apr 3, 2025 · Dejan Murko

Cybersecurity for Freelancers
Freelancers face credential theft, phishing, and breach risks without a corporate IT team. Here are practical cybersecurity steps every freelancer can take this week.
Mar 13, 2025 · Dejan Murko

Cybersecurity for Remote Workers
Remote work expands an organization attack surface — hackers target unprotected home setups. Here are practical cybersecurity steps every remote worker should take today.
Feb 27, 2025 · Dejan Murko
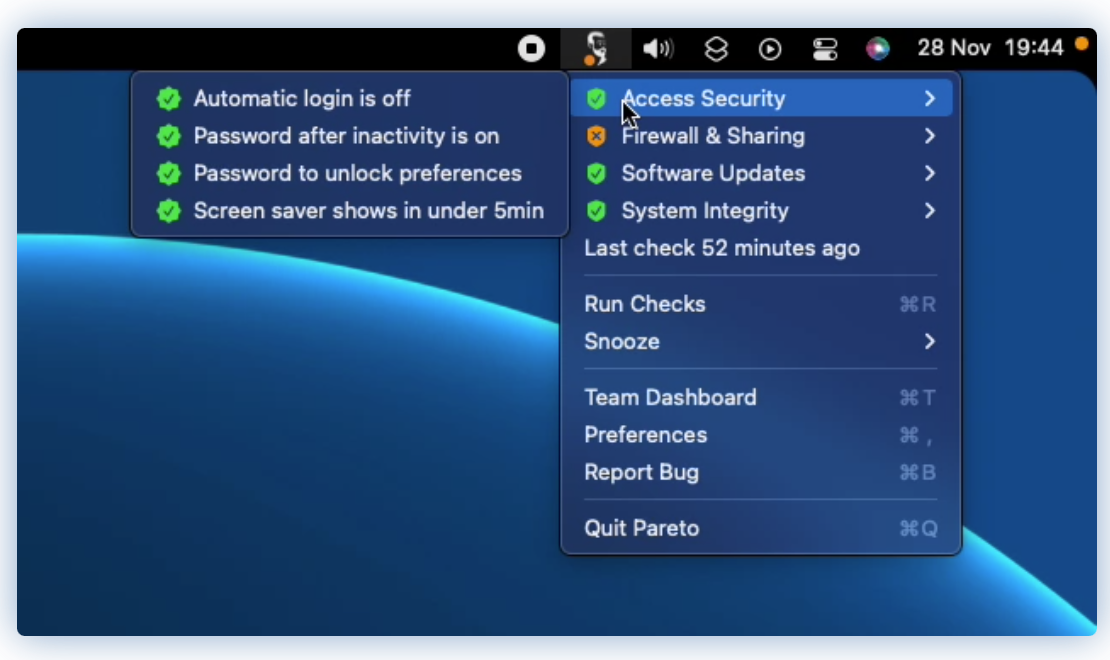
Netflix Stethoscope deprecation and alternatives
Netflix's Stethoscope was an open-source project for enhancing endpoint security in a user-focused and non-intrusive manner. It was built by the Netflix...
Nov 16, 2023 · Dejan Murko

Cyber Security Checklist for Macs
In this topic we’ll cover the basic Mac cyber security checklist. Macs have great security options out-of-box but not all of them are configured.
Apr 8, 2022 · Dejan Murko

Cyber Security Self-Assessment
Protecting your critical data and information from malicious parties is a key responsibility for business owners. Companies need to budget for cybersecurity...
Oct 12, 2021 · Dejan Murko